Social Media Threats, Attacks & Security | Risks of Social Media - Video & Lesson Transcript | Study.com

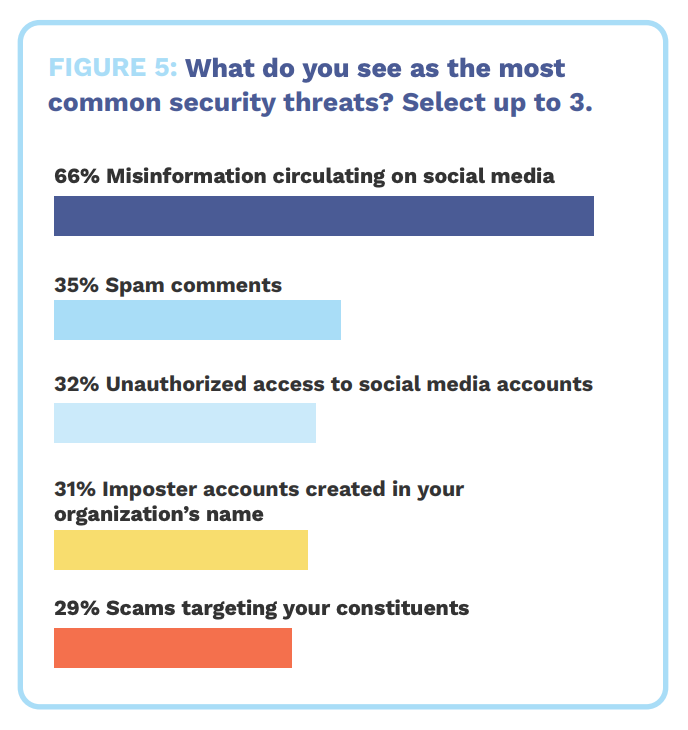
Threats percentage-pose on social networks (Sophos 2010 Security Threat... | Download Scientific Diagram

Social Media: The Threats While Using Social Media Accounts - Institute of Entrepreneurship Development